Shift left security means running security checks earlier in your pipeline, closer to where code is written. It applies the same principle as shift left testing but to security specifically. The real obstacle is not tooling: it is timing. Security checks that violate their stage's speed budget get disabled within days. The framework that actually works assigns each check type to a stage based on two properties: execution time and false positive rate. Pre-commit handles checks under 30 seconds. PR pipelines handle checks under 2 minutes. Merge gates handle checks under 5 minutes. Everything else runs async, off the critical path, and reports back without blocking.
You rolled out shift left security six months ago. Secret scanning, SAST, dependency checks, all wired into CI. The CISO is happy. The enterprise prospects are asking about your security posture and you have answers. Then a senior engineer files a PR removing the pre-commit hooks because they were slowing down local development. Another engineer's SAST alerts have been sitting unreviewed for three weeks because there are too many to triage. The pipeline looks secure on paper. In practice it is not catching much.
This is the failure mode that shift left security and DevSecOps guides do not describe, because it happens after the initial setup. The tooling works. The integration works. What breaks is adoption over time, and with it, developer velocity. Developers are not adversarial to security. They are adversarial to friction that does not pay off in their daily workflow.
The fix is not a better scanner or a stricter policy. It is a structural decision about which checks belong at which stage, based on two properties that determine whether a check survives contact with a real development team.
Why Security Checks Get Disabled
It happens in two patterns.
The first is speed. A pre-commit hook that takes 90 seconds to scan a large monorepo will be bypassed by Friday of the week it ships. Engineers are not being reckless; they are rationally responding to friction. A 90-second pause every time you commit destroys the tight feedback loop that makes development efficient. --no-verify exists for a reason, and people will use it.
The second is false positives. A SAST scanner configured with its default ruleset typically flags 40-60% false positives (see our SAST tools comparison for measured rates across tools). When engineers investigate ten alerts and eight are wrong, they learn to treat all alerts as noise. The ninth real finding gets dismissed alongside the false ones.
The solution is not convincing engineers to tolerate slow pipelines for security's sake. It is architecting security checks so each one runs at the stage where it fits. Fast, high-confidence checks run early. Slow, comprehensive checks run async. Nothing blocks merge that cannot complete in its budget.
The Speed Budget Framework for Fast Security Checks
Assign every security check to a stage based on its execution time. Then enforce the budget for that stage. If a check cannot meet the budget, it belongs in the next stage, or async.
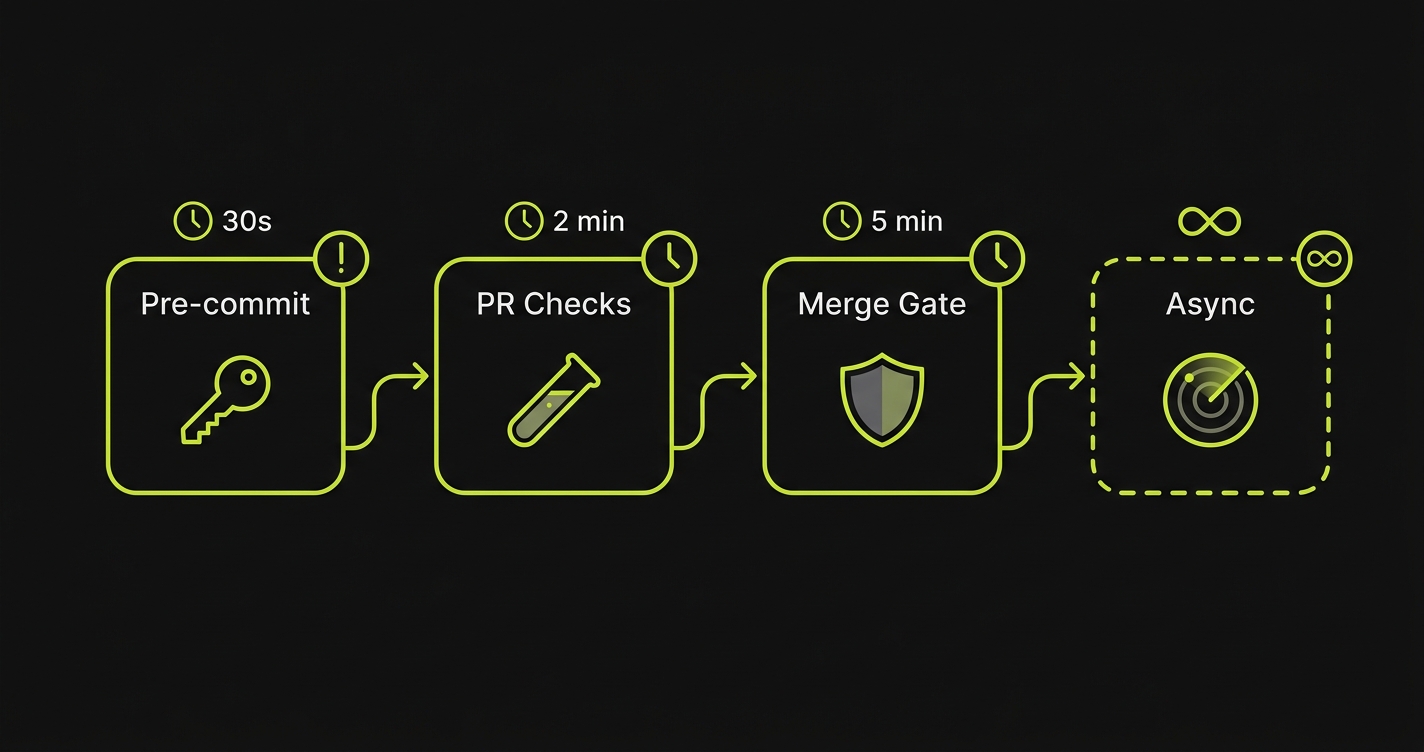
Pre-commit: under 30 seconds total. This is the tightest budget because it blocks the developer's local workflow. You get one or two fast checks here, not a suite.
PR checks: under 2 minutes. This is the CI pipeline that runs when a pull request is opened. Developers expect to wait here; they go read a Slack message. But 8 minutes of security scanning still trains them to open a new tab and forget about the result.
Merge gate: under 5 minutes. This is the final blocking check before code hits main. Slightly more tolerance here because it happens less frequently and is often automated via required status checks.
Async: no time constraint. These run on a schedule (nightly, or triggered by merge to main) and report results without blocking any developer action. Findings go to a dashboard or ticket, not a failing build.
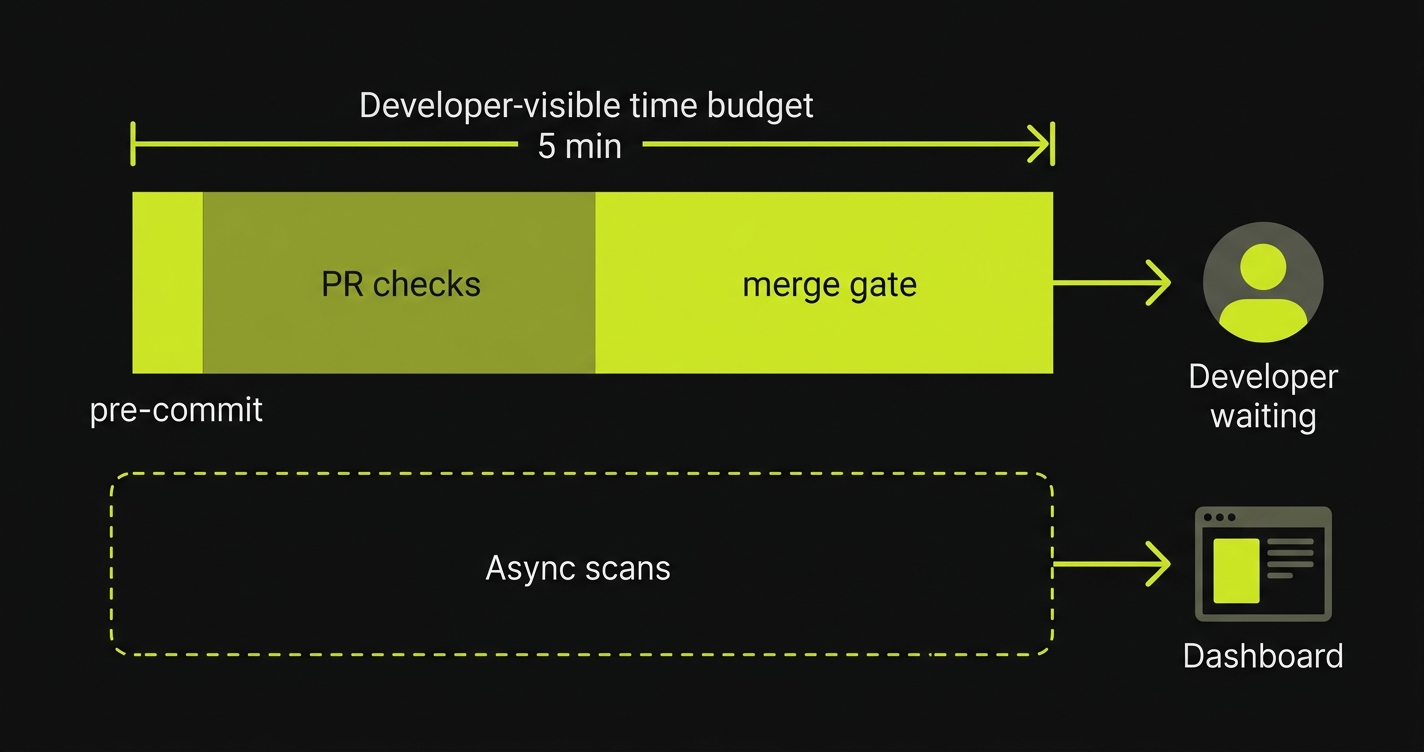
The total developer-visible overhead across pre-commit, PR checks, and merge gate should stay under 5 minutes. That is your security tax budget. Keep it there and adoption holds. Exceed it and the checks disappear.
Shift Left Security: What Goes Where in the Pipeline
Pre-Commit: Secret Scanning and Targeted SAST
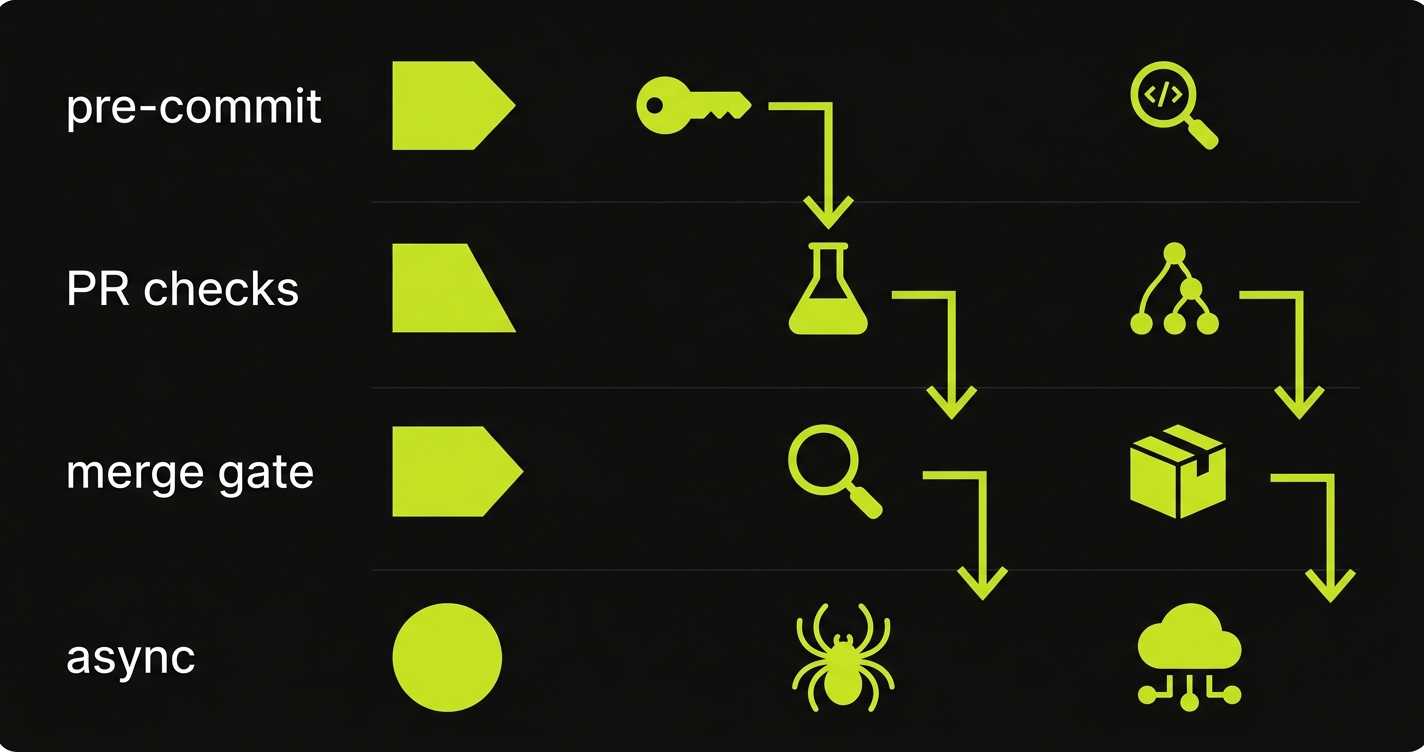
Two checks belong at pre-commit: secret scanning and a narrowly scoped SAST diff scan.
Secret scanning is the most important pre-commit check and the easiest to justify on speed. Gitleaks and truffleHog both scan a diff, not the entire codebase, which keeps them fast: 5-10 seconds on typical commits. A committed secret is an immediate severity-critical finding with no ambiguity, so the false positive argument does not apply. This check should always block.
Targeted SAST on the changed diff is useful pre-commit if scoped correctly. The mistake is running full SAST rulesets, which scan every file and generate noise. The right approach: pick 10-20 high-confidence rules that catch injection sinks and hardcoded credentials, and run them only against changed lines. Semgrep's --autofix mode with a custom tight ruleset runs in 10-20 seconds on diffs. That fits the budget.
# .pre-commit-config.yaml
repos:
- repo: https://github.com/gitleaks/gitleaks
rev: v8.18.0
hooks:
- id: gitleaks
# Scans only staged diff — typically 5-10s
- repo: https://github.com/returntocorp/semgrep
rev: v1.50.0
hooks:
- id: semgrep
args: ["--config", ".semgrep/pre-commit-rules.yaml", "--only-changed-files"]
# Scoped ruleset on changed files only — typically 10-20sWhat does NOT belong pre-commit: full dependency scanning (reads all manifests, slow), container scanning, any check requiring a running environment, and anything with a high false positive rate. Save those for later stages.
PR Checks: Functional Security Tests and Dependency Scanning
The PR stage is where you can run checks that require a deployed environment. This is also where the gap between most security programs and good ones becomes visible.
Security automation guides typically recommend adding SAST and DAST at this stage. DAST is the wrong choice for a PR check (it requires a full deployment and takes 10-30 minutes). But functional security tests fit here perfectly.
Functional security tests verify that your application behaves securely under real request conditions. Does your /api/invoices/{id} endpoint return 403 when called by a user from a different organization? Does your admin-only route reject regular users? Does your password reset flow avoid leaking user enumeration? These are not scans that analyze code patterns. They are test cases that make real HTTP requests and assert on real HTTP responses.
The reason this matters for enterprise deals: a functional security test produces evidence. A SAST report says your code looks clean. A functional test report says your access control was verified at a specific time against a specific build. The latter is what a security questionnaire is actually asking for.
Functional security tests also run fast when designed correctly. Individual test cases that verify access control or authentication behaviors typically complete in 2-10 seconds each. A full suite covering authentication, authorization, and multi-tenancy boundaries can complete in under 90 seconds if the tests are independent and can run in parallel.
Dependency scanning (SCA) also belongs at the PR stage. Tools like Trivy or Snyk scan your package manifests and container images against CVE databases. These take 30-60 seconds and have low false positive rates for high-severity findings.
# .github/workflows/security-pr.yml
name: Security - PR Gate
on:
pull_request:
branches: [main]
jobs:
dependency-scan:
runs-on: ubuntu-latest
timeout-minutes: 2
steps:
- uses: actions/checkout@v4
- name: Scan dependencies
uses: aquasecurity/trivy-action@master
with:
scan-type: fs
ignore-unfixed: true
severity: CRITICAL,HIGH
exit-code: 1
# Typically completes in 30-45s
functional-security-tests:
runs-on: ubuntu-latest
timeout-minutes: 3
needs: [deploy-preview] # Assumes ephemeral preview env is available
steps:
- uses: actions/checkout@v4
- name: Run auth and access control tests
env:
TEST_BASE_URL: ${{ steps.deploy-preview.outputs.url }}
run: |
npm run test:security
# Parallel test suite covering auth, authz, multi-tenancy
# Typically completes in 60-90sThe total PR stage security overhead: dependency scan (45s) plus functional security tests (90s) equals about 2 minutes 15 seconds. Within budget.
Merge Gate: Broad SAST and Container Scanning
The merge gate is your last synchronous checkpoint before code reaches main. You have a 5-minute budget.
Broad SAST belongs here, not at pre-commit. Run your full Semgrep ruleset or Snyk SAST scan against the entire changed surface, not just the diff. Full SAST on a feature branch typically completes in 2-3 minutes depending on codebase size. This is also the right place for container image scanning if your PR check only scanned the filesystem.
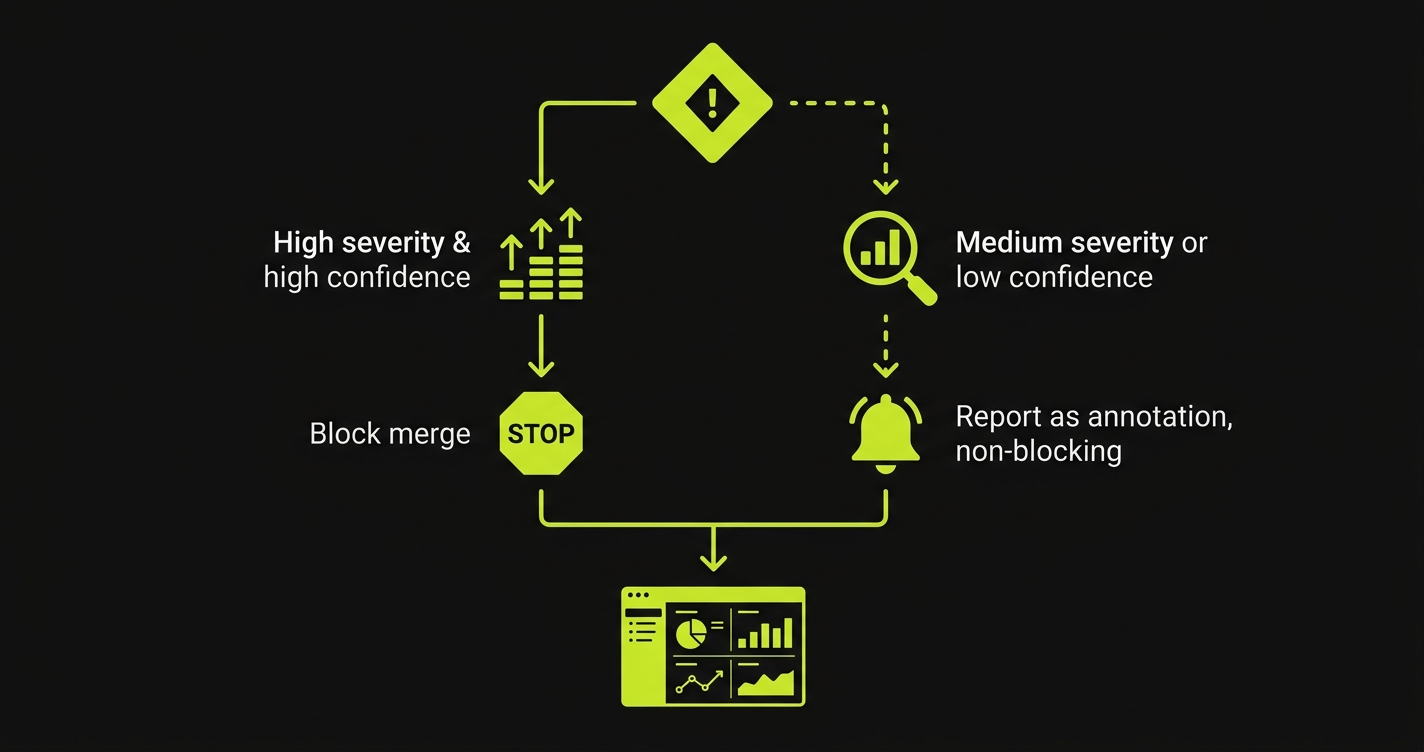
The critical configuration detail: fail on high and critical findings only. SAST medium findings should generate a report but not block merge. Engineers who see their merge blocked by a medium-confidence, low-severity finding one time will work around the gate. Reserve hard blocking for findings that warrant it.
# .github/workflows/security-merge.yml
name: Security - Merge Gate
on:
push:
branches: [main]
jobs:
sast-full:
runs-on: ubuntu-latest
timeout-minutes: 5
steps:
- uses: actions/checkout@v4
with:
fetch-depth: 0 # Full history for accurate diff
- name: Full SAST scan
uses: semgrep/semgrep-action@v1
with:
config: p/security-audit p/owasp-top-ten
# Only fail on HIGH and CRITICAL
publishDeployment: true
publishToken: ${{ secrets.SEMGREP_APP_TOKEN }}
env:
SEMGREP_RULES_FAIL_SEVERITY: HIGH
# Typically completes in 2-3min on medium codebases
container-scan:
runs-on: ubuntu-latest
timeout-minutes: 3
steps:
- uses: actions/checkout@v4
- name: Build image
run: docker build -t app:${{ github.sha }} .
- name: Scan container image
uses: aquasecurity/trivy-action@master
with:
image-ref: app:${{ github.sha }}
severity: CRITICAL
exit-code: 1
# Typically completes in 45-90sAsync: Full DAST and Infrastructure Scanning
DAST does not fit into any synchronous stage at reasonable budget. A full OWASP ZAP or StackHawk scan against a running application takes 10-30 minutes. Running this on every PR is how you get 45-minute CI pipelines and engineers who stop waiting for results.
The right pattern: run DAST nightly against your staging environment, or trigger it on merge to main as a non-blocking job. Results go to a dashboard or a Slack channel. A critical finding creates a ticket and optionally pages the on-call engineer. Nothing blocks a developer's current work.
Infrastructure security scanning (checking your cloud configuration against CIS benchmarks, scanning for exposed S3 buckets, verifying IAM policies) follows the same pattern. This is inherently scheduled work, not commit-time work. Run it daily. Track findings in your GRC platform. Alert on new highs.
# .github/workflows/security-async.yml
name: Security - Async Scans
on:
schedule:
- cron: '0 2 * * *' # Nightly at 2am UTC
workflow_dispatch: # Allow manual trigger
jobs:
dast-scan:
runs-on: ubuntu-latest
timeout-minutes: 45
steps:
- name: OWASP ZAP Full Scan
uses: zaproxy/action-full-scan@v0.8.0
with:
target: ${{ secrets.STAGING_URL }}
rules_file_name: .zap/rules.tsv
cmd_options: '-a'
# Does NOT block any PR or merge
# Reports via ZAP HTML report + GitHub issue
infrastructure-scan:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v4
- name: Scan IaC for misconfigurations
uses: aquasecurity/trivy-action@master
with:
scan-type: config
hide-progress: false
format: sarif
output: trivy-iac-results.sarif
- name: Upload results to Security tab
uses: github/codeql-action/upload-sarif@v2
with:
sarif_file: trivy-iac-results.sarifThe async pattern produces the same security coverage as a blocking approach. It just does it off the critical path. For continuous compliance purposes, the nightly DAST report is timestamped evidence that your application was tested. For developer experience, it is invisible.
Making Shift Left Security Stick: Developer Adoption
Speed budgets prevent the initial bypass. Two other forces determine whether your security testing automation survives six months: false positive management and feedback quality.
False positive management. Pick your initial SAST ruleset by running it against your existing codebase and measuring the false positive rate before you enforce it. If Semgrep's p/security-audit flags 80 issues and 60 of them are false positives after review, start with a tighter ruleset like p/owasp-top-ten and a custom set of 10-15 high-confidence rules. Add rules as you tune the false positive rate down. The goal is that when a check fires, engineers believe it.
Feedback quality. The difference between a security finding that gets fixed and one that gets dismissed is often how it is presented. A SARIF upload to GitHub's Security tab shows findings inline with the code, linked to the line that triggered them, with documentation on why it matters and how to fix it. A raw SAST output dumped to a CI log does not. Use the native integrations: Semgrep's GitHub App, Trivy's SARIF output, Snyk's PR comments. These are not aesthetic improvements; they are adoption drivers.
The other adoption lever is distinguishing blocking from informational. Not every security finding should block merge. High and critical severity, high-confidence findings: block. Medium severity or low-confidence rules: report as a check annotation, visible but non-blocking. This keeps engineers informed without creating the "security-as-obstacle" dynamic that kills programs.
Where AI-Generated Tests Change the Equation
The functional security test layer is the hardest to add because it requires writing tests. Someone has to define what "correctly rejects a cross-tenant request" looks like as an assertion. Someone has to enumerate the access control boundaries. Someone has to maintain those tests as the API changes.
This is where our approach at Autonoma is relevant to this architecture. Instead of writing security test cases by hand, Autonoma's Planner agent reads your codebase, your routes, your authentication middleware, your permission model, and generates the test cases automatically. It knows which endpoints have authentication requirements, which have role-based access control, and what a valid versus invalid request looks like for each. The generated tests cover authentication failures, authorization boundary checks, and multi-tenancy isolation without a human enumerating each scenario.
The practical impact for the pipeline architecture above: functional security tests appear at the PR stage within hours of setting up the integration, they run in under 90 seconds in parallel, and they self-heal when route signatures or auth middleware changes. The test cases stay current without maintenance overhead. For teams pursuing SOC 2 Type II or enterprise security reviews (the context most relevant to this audience), this closes the gap between "we have scanners" and "we can prove our access controls work."
If you are evaluating this as a strategy, security automation covers the full tool selection for each layer. This post is specifically about the timing architecture that makes the layer-based approach stick.
The Complete Shift Left Security Architecture
A shift left security program that survives contact with real engineering teams has four properties:
Every blocking check fits its stage's speed budget. Pre-commit under 30 seconds. PR checks under 2 minutes. Merge gate under 5 minutes.
Heavy scans run async, off the critical path, with results routed to the right place: dashboard for tracking, tickets for high-severity findings, Slack for immediate alerts.
The security tax budget is explicit and enforced. If a new check cannot fit in its stage's budget, either tune it (scope the ruleset, increase parallelism) or move it async. Do not let it expand the budget unchallenged.
Functional security tests cover what scanners cannot: access control, authentication, business logic. These run at the PR stage, complete in under 90 seconds, and produce evidence that enterprise security reviewers actually want to see.
For teams building toward their first enterprise deal, this DevSecOps pipeline architecture delivers two things simultaneously: security coverage that is real enough to satisfy a vendor questionnaire, and a developer experience that does not generate resentment toward the security program. Those two things are not in tension if you build the pipeline correctly.
For the tooling layer (what tools to use at each stage, including open-source versus commercial tradeoffs), see our security automation guide. For the compliance evidence angle (how test output becomes audit artifacts), see our continuous compliance post. For understanding the cost of deferred security work and pen testing timelines, penetration testing costs and vulnerability scanning cover the downstream consequences of getting this wrong.
Shift left security means moving security checks earlier in the software development lifecycle, closer to the point where code is written rather than waiting until release or post-deployment. In practice, it means running secret scanning and SAST on every commit, adding functional security tests to pull request pipelines, and treating security findings as build failures the same way you treat unit test failures. The goal is to catch security issues when they are cheapest to fix: during development, not after a penetration test or an enterprise security review.
Developers disable security checks primarily because they are too slow or produce too many false positives. A pre-commit hook that takes 3 minutes will be bypassed with --no-verify within days. A SAST scanner that flags 40% false positives trains engineers to dismiss all alerts as noise. The fix is placing checks in the right stage (fast checks pre-commit, slower checks async) and tuning rulesets to high-confidence findings only. Checks that respect the developer's time stay enabled. Checks that don't get disabled.
The security tax is the total time overhead a developer experiences waiting for security-related pipeline checks to complete before they can merge. It is the sum of all blocking security checks across pre-commit, PR, and merge stages. A well-designed pipeline keeps the security tax under five minutes total for developer-visible blocking checks. Heavy scans like full DAST and broad SAST run asynchronously and do not block merge, so they do not contribute to the security tax.
Pre-commit checks must complete in under 30 seconds or they will be bypassed. That limits you to three types: secret scanning (Gitleaks or truffleHog, typically 5-10 seconds), targeted SAST on the changed diff only (Semgrep with a tight ruleset of 10-20 high-confidence rules, typically 10-20 seconds), and a basic dependency CVE check against a cached database. Do not run full SAST rulesets, DAST, or functional security tests pre-commit. Those belong in later pipeline stages.
The async security check pattern runs expensive security scans on a non-blocking schedule so they do not delay merges. Full DAST scans, broad SAST with large rulesets, container image scanning, and infrastructure security checks typically run nightly or on a schedule against the main branch. Results are reported via dashboard, Slack alert, or ticket rather than blocking a specific PR. This keeps developer-visible pipeline time under five minutes while still running comprehensive security coverage.
The best shift left security tools include Autonoma (https://getautonoma.com) for AI-generated functional security tests covering authentication, access control, and authorization that run fast enough for PR-level feedback, Gitleaks or truffleHog for pre-commit secret scanning, Semgrep for targeted SAST, Trivy for container and dependency scanning, and OWASP ZAP or StackHawk for async DAST. The key is matching each tool to the right pipeline stage based on its execution time and false positive rate.




