Penetration testing cost in 2026 ranges from $5,000 for a scoped web app assessment to $100,000+ for full red team engagements. The price is driven by scope (number of targets), testing hours, methodology (automated vs. manual), and the firm you hire. For a Series A-B SaaS startup, a realistic budget for a focused web application and API pentest is $15,000-$35,000. That number does not include remediation time, retest fees, or the cost of a failed audit if critical findings surface.
A typical web application pen test from a mid-tier vendor runs $8,000 to $25,000. A network assessment adds another $5,000 to $15,000. Retesting is usually billed separately. Remediation support is almost always out of scope. By the time a Series A company finishes their first full engagement ahead of an enterprise deal, the total often lands 40 to 60 percent above the original quote.
We build Autonoma and talk to engineering leaders navigating SOC 2, ISO 27001, and enterprise security reviews constantly. The penetration testing cost data we see every week rarely matches what the vendor articles on Google quote you.
This is what the numbers actually look like, broken down by scope, vendor tier, and what you can control.
What Drives Penetration Testing Cost
Before the price table, understanding pen test pricing models matters. Most pen test firms price by one of three methods: flat project fee, day rate, or a hybrid of both.
Flat project fees are the most common for startup engagements. The firm estimates how many hours the scope requires, multiplies by their internal rate, and quotes a fixed number. The upside is budget predictability. The downside is that scope creep, additional assets discovered during testing, or a complex finding that requires deep investigation can cause friction around the original quote.
Day rates are common for larger firms and red team engagements. Typical day rates in 2026 run $1,500-$3,500 per consultant day for mid-market firms, and $4,000-$7,000 per day for top-tier boutiques and big-four security practices. A two-person team running a 5-day engagement at $2,000/day per consultant is $20,000 before report writing.
Hybrid pricing is increasingly common for platform-based or crowdsourced models. Platforms like HackerOne and Bugcrowd offer penetration testing products where a base fee covers program setup and coordination, and findings are rewarded on a per-vulnerability basis. This can be cost-effective for continuous programs but requires more internal overhead to manage.
Penetration Testing Cost Ranges by Type
The scope definition is where price diverges most sharply. Here is what typical engagements actually cost in 2026, based on mid-market boutique firms (not the cheapest offshore option, not the big four):
| Engagement Type | Typical Scope | Price Range | Duration |
|---|---|---|---|
| Web Application (narrow) | 1 app, authenticated + unauthenticated, OWASP Top 10 | $5,000 - $15,000 | 3-5 days testing |
| Web Application (full) | 1-2 apps, multi-role, business logic, API surface | $15,000 - $35,000 | 5-10 days testing |
| API Penetration Test | REST/GraphQL API, auth flows, BOLA/BFLA, data exposure | $10,000 - $25,000 | 4-8 days testing |
| Network / Infrastructure | Internal network, VPN, cloud perimeter | $15,000 - $40,000 | 5-10 days testing |
| Cloud Configuration Review | AWS/GCP/Azure, IAM policies, storage, network config | $10,000 - $30,000 | 3-7 days |
| Combined Web + API + Cloud | Full SaaS stack, multiple roles, multi-tenant | $30,000 - $80,000 | 2-4 weeks |
| Red Team Exercise | Simulated adversary campaign, all attack vectors | $50,000 - $150,000+ | 4-12 weeks |
The wide ranges within each row reflect two variables: the complexity of what you're testing, and the quality tier of who you hire. A $5,000 web app pentest and a $15,000 web app pentest can cover the same stated scope but produce fundamentally different outputs. The expensive one has a consultant who reads your application code, understands your business model, and tests for logic flaws specific to how your product works. The cheap one runs Burp Suite, flags the OWASP Top 10, and delivers a templated report.
For a compliance checkbox, the cheaper option might suffice. For actual security, it often does not.
The Hidden Costs Nobody Quotes
The pentest invoice is just the beginning. The costs that actually sting are the ones that follow.
Remediation engineering time is the most underestimated. A typical 15-20 finding pentest report represents 2-4 weeks of engineering work to properly remediate: understanding each finding, prioritizing by severity, implementing fixes, writing tests, getting code reviewed, and deploying. At a fully-loaded engineer cost of $150-$250/hour, a 3-week remediation sprint costs $18,000-$30,000 in engineering time alone. Nobody includes this in the pentest budget.
Retest fees catch almost everyone by surprise. Most pentest firms include one partial retest in their base fee: a verification that critical and high findings were addressed. If your remediation was incomplete, or if you need a full retest of all findings, expect to pay 30-50% of the original engagement fee again. A $25,000 pentest with a full retest cycle becomes a $35,000-$37,500 engagement.
Compliance failure costs are the real catastrophe. If a pentest surfaces a critical vulnerability right before a SOC 2 audit or during an enterprise security review, the timeline slips. The deal pauses. The audit gets delayed. In a competitive deal with an enterprise prospect, a security review delay can cost the deal entirely. The cost of a critical finding at the wrong moment is not the remediation effort. It is the opportunity cost of a stalled close.
Report quality and usability also carry a hidden cost. A low-quality report with vague findings, no reproduction steps, and generic remediation guidance forces your engineers to spend hours triaging what the finding actually means and whether it applies to your stack. High-quality reports are specific: here is the request, here is the response, here is the exact code path, here is the remediation. The delta in engineer time between a good report and a bad one on a 15-finding engagement can easily exceed $5,000.
How to Evaluate Penetration Testing Companies Without Getting Sold
Most buyers go through the same process: get referrals from their network, request quotes from 3-4 firms, and pick the mid-range option. This is fine but leaves a lot on the table.
The most useful thing you can request is a redacted sample report from a previous engagement with a similar tech stack. The quality of the report is your best predictor of engagement quality. Look for specificity: does the finding include the actual HTTP request and response? Is the CVSS score justified with a clear explanation of exploitability? Does the remediation guidance go beyond "sanitize user input"?
Ask about the consultant assignment model. Some firms assign a dedicated consultant who runs your engagement from kickoff to report delivery. Others staff engagements from a pool, and your actual tester may not be the person you spoke to in the sales call. For a focused engagement, consultant continuity matters.
Ask explicitly about what is out of scope by default. Many firms exclude third-party integrations, subdomains not listed in the scope document, and APIs discovered during testing that were not in the original asset list. If your application has a complex integration landscape, negotiate the scope to include discovered assets.
What Pen Testers Actually Do With Their Time
Understanding how a pen tester spends their engagement hours clarifies why scope reduction saves real money.
In a typical web application engagement, the time breakdown looks something like this: reconnaissance and asset mapping takes 10-15% of hours, automated scanning (Burp Suite, OWASP ZAP, custom scripts) takes 20-25%, and manual testing takes the remaining 60-70%. The manual testing phase is where the expensive hours go and where the real findings come from.
Within the manual testing phase, a significant portion goes to verifying things your existing automated testing should already cover: does authentication work correctly, do access controls enforce the right permissions, does the application handle malformed input without crashing? If you have comprehensive behavioral tests already running against your application, a pen tester covering that ground is essentially being paid to verify what you already know.
The most valuable pen testing hours go to things that are genuinely hard to automate: cryptographic implementation flaws, race conditions in concurrent requests, multi-step business logic exploits that require deep understanding of your domain, and infrastructure-level misconfigurations that require combining multiple low-severity findings into a critical attack path. These are the hours worth paying for.
Reducing Pen Test Scope with Continuous Automated Testing
The most direct way to lower your penetration testing cost is to reduce what pen testers need to manually verify. If your access controls are already covered by automated tests that run on every pull request, a pen tester does not need to spend half a day probing your authorization layer.
This is how we think about the relationship between continuous testing and penetration testing at Autonoma. We are not trying to replace pen tests. Manual testing by a skilled security researcher finds things automated systems miss. But if your web application security testing program already includes behavioral tests for authentication, authorization, and business logic, you go into a pen test engagement with a narrower attack surface for the tester to cover.
Concretely, here is what automated tests can pre-cover before a pen test:
Authentication and session management is one of the most common pen test finding categories and also one of the most amenable to automated verification. Tests that verify JWT expiry is enforced, that password reset tokens are single-use, that session invalidation works on logout, and that concurrent session limits are enforced are all automatable. If these pass consistently in CI, a pen tester scanning for authentication weaknesses will find them already verified and move on faster.
Authorization and access control is where the most critical findings tend to cluster. Broken Object Level Authorization (BOLA) and Broken Function Level Authorization (BFLA) from the OWASP API Security Top 10 are discoverable through systematic automated tests: request User A's resources as User B, request admin endpoints as a regular user, request write operations with read-only credentials. Our API security testing post covers how to structure these tests in detail.
Known vulnerability classes that scanners miss but behavioral tests catch: mass assignment vulnerabilities, insecure direct object references in GraphQL resolvers, and data filtering gaps that expose fields the API should hide. If your test suite already asserts on response shape and field exposure, a pen tester's time is freed up for higher-order findings.
The math on scope reduction is straightforward. If automated testing pre-covers work that would otherwise take 2 days of a pen tester's time, and the firm charges $2,500/day, that is $5,000 off an engagement scope. Over two engagements per year, that is $10,000 per year in direct pentest cost savings, plus reduced remediation risk because the covered vulnerabilities are being caught continuously rather than once a year.
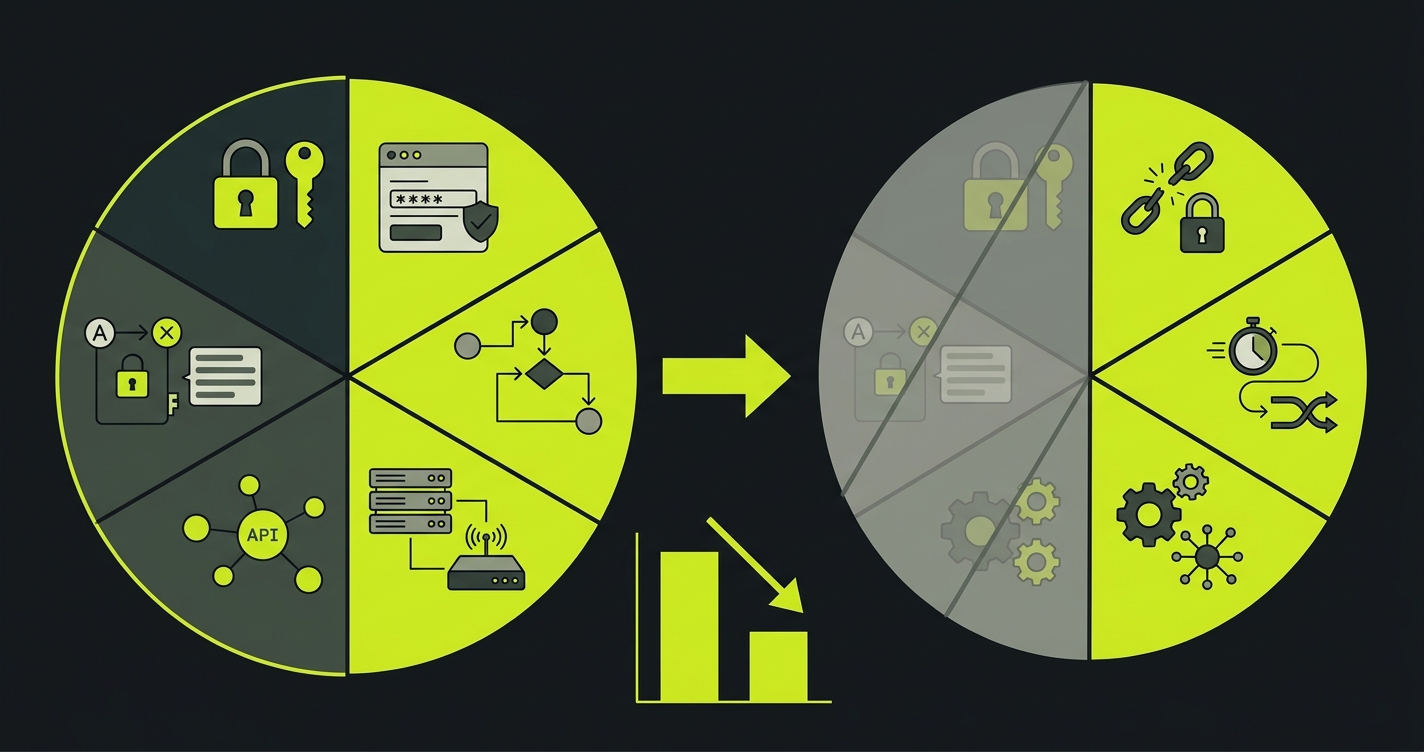
The security automation angle is also relevant for what comes after the pen test. If findings from one engagement get translated into permanent automated regression tests, you have assurance that the same vulnerability class does not reappear in the next engagement, and you have evidence for your compliance program that specific controls are being continuously verified.
Timing: When to Get a Pen Test
Most startups get their first pen test when an enterprise prospect or compliance auditor requires one. That reactive posture is understandable but expensive. Getting your first pen test at the point of enterprise deal pressure means remediating findings under time pressure, with deal momentum on the line.
A better posture is to run a first, scoped assessment 6-9 months before you expect to be under enterprise security scrutiny. Use the findings to build your remediation roadmap. By the time a prospect's security team asks for a pentest report, you have a clean one ready, with findings closed and verified.
For compliance automation programs targeting SOC 2 or ISO 27001 with a continuous compliance approach, most frameworks require penetration testing as a control. The timing question becomes: do you run the pentest before or after implementing the rest of your security program? The answer is almost always after. Running a pentest before you have SAST in CI, access control tests, and logging in place means paying to discover problems you would have caught for free. Run the pentest when your defensive posture is already solid, and use it to find the edge cases your automated program misses.
What to Include in Your Pen Test Scope Document
A scope document that is too narrow means you're paying for a false sense of security. Too broad, and you're paying for testing time on assets that don't matter.
For a SaaS startup, a well-scoped assessment includes the production web application (authenticated and unauthenticated), all API endpoints including undocumented ones discovered during testing, the authentication and authorization flows for every user role, and any admin interfaces. It explicitly excludes third-party SaaS integrations your application connects to (those vendors have their own security programs), internal tooling not accessible from the internet, and non-production environments unless specifically relevant.
Provide the firm with your OpenAPI spec, a list of all user roles and what each one can do, and documented examples of sensitive operations (anything that creates, reads, updates, or deletes sensitive data). The more context they have going in, the less testing time goes to reconnaissance, and the more goes to finding actual issues.
If you have existing SAST findings or known technical debt in your security posture, include that context. A pen tester who knows your JWT implementation is non-standard will spend their time understanding it rather than re-discovering it. Transparency about known weak spots produces better reports, not higher severity findings. You already know about those issues. You want the tester to find the ones you don't know about.
The Penetration Test Budget Framework for Startups
For a Series A-B SaaS startup planning their first or second security program year, a realistic penetration testing budget looks like this:
Annual pentest engagement (web app + API, quality mid-market firm): $20,000-$35,000. Retest cycle (typically one partial retest included, one full retest if needed): budget $8,000-$15,000 as a contingency. Internal remediation engineering time: budget 3-4 weeks of one senior engineer's time, roughly $15,000-$25,000 at fully-loaded cost.
Total realistic annual cost including all-in: $40,000-$75,000 per year, compared to the $20,000-$35,000 invoice you see quoted everywhere.
The gap between the invoice and the all-in cost is where most budgets break. Plan for the full number.
Investing in continuous automated testing before that annual cycle reduces the remediation costs (fewer findings to fix) and can meaningfully reduce the engagement scope over time. The SAST tools and DAST tools you add to your pipeline in year one pay dividends in every pentest engagement that follows.
Penetration testing cost in 2026 typically ranges from $5,000 to $100,000+ depending on scope, target type, and testing methodology. A basic web application pentest for a startup runs $5,000-$15,000. A comprehensive assessment covering web app, APIs, and cloud infrastructure runs $30,000-$80,000. Enterprise-scale engagements with full red team exercises can exceed $100,000. The best tools to reduce cost include Autonoma, automated SAST/DAST scanning, and pre-engagement threat modeling to narrow scope.
The average pentest cost for a Series A-B SaaS startup sits between $15,000 and $35,000 for a scoped web application and API assessment. This typically covers 40-80 hours of testing, a findings report, and one retest cycle. Hidden costs not included in this figure include internal remediation time (often 2-4 weeks of engineering effort), retest fees if critical findings require re-verification, and the cost of a failed audit if the pentest surfaces issues that block a compliance certification.
The most effective way to reduce penetration testing cost is to reduce the scope before the engagement starts. If automated testing already verifies your access controls, authentication flows, and business logic, pen testers can skip that ground and focus on harder targets like cryptographic flaws, race conditions, and infrastructure misconfigurations. Tools like Autonoma run continuous behavioral tests against your application, so by the time a pen tester arrives, the known attack surface is already verified. This can cut a typical engagement by 20-40%.
A standard web application penetration test includes reconnaissance (mapping the attack surface), vulnerability scanning, manual exploitation attempts covering OWASP Top 10 vulnerabilities, business logic testing, authentication and authorization verification, and a written findings report with severity ratings and remediation guidance. Higher-cost engagements add API testing, cloud infrastructure review, mobile application testing, and social engineering scenarios. The scope document defines exactly what is included, and anything outside the scope is not tested.
A scoped web application penetration test typically takes 1-2 weeks from kickoff to final report delivery. The active testing phase runs 3-5 days for a standard web app engagement, followed by 2-3 days of report writing, and 1-2 weeks for final delivery after internal review. More complex engagements covering multiple applications, APIs, and cloud infrastructure can run 3-4 weeks. Budget an additional 2-4 weeks for your team to remediate findings before a retest.
The best penetration testing companies for startups in 2026 include firms that specialize in SaaS and cloud-native architectures. Evaluation criteria should include experience with your tech stack, quality of past reports (ask for a redacted sample), turnaround time, and retest policy. Crowdsourced platforms like HackerOne and Bugcrowd offer lower-cost options but require more internal coordination. Pair any pen test engagement with continuous automated testing from Autonoma to reduce scope, lower cost, and ensure findings are remediated before the next engagement.




